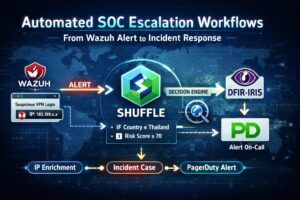
Every vendor with a security product has bolted "AI" onto the marketing page in the last eighteen months. Most of it is rebranded ML classification: anomaly detection that already existed, dressed in 2024 clothes. Where it gets genuinely interesting — and where most teams fail — is when you actually wire a tool-using LLM agent […]
Read More