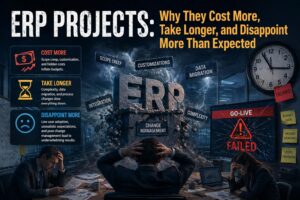
Enterprise ERP integration is a solved problem — at least, that’s what your SI vendor will tell you. The reality inside tier-2 and tier-3 manufacturing plants is very different: brittle point-to-point connectors, hand-rolled ABAP scripts, and decades-old middleware that breaks every time a vendor pushes a schema update. The data exists. The systems exist. The […]
Read More